On Our Radar 🎯
The Government Told You to Use a VPN. They Also Admit It May Strip Your Constitutional Rights.
Four senators and two representatives sent a letter to Director of National Intelligence asking her to publicly disclose whether Americans using commercial VPNs are being treated as foreigners under US surveillance law. The idea goes like this: if a VPN routes traffic through another country, the NSA may treat that traffic as foreign, classify the user as a non-US person, and strip the constitutional protections against warrantless surveillance they're entitled to as Americans. (which we already feel is questionable at best).
This all happens under Section 702 of FISA, which enables the NSA to warrantlessly collect communications of people abroad. The lawmakers aren't claiming this VPN scenario has definitively happened—that info is classified. But the fact they're asking at all is a pretty obvious signal it's something we should watch out for.
What you can do: Big story...I have some takeaways:
- No individual action eliminates this risk, it's a structural legal issue. What you can do is contact your representatives and tell them Section 702 reform matters to you. Organizations like EFF are actively campaigning against this.
- This story exposes a deeper flaw in how governments approach digital rights: the belief that we can draw jurisdictional lines around data that flows globally by design. But the real fix isn't a carve-out restoring American rights—it's recognizing that mass surveillance is wrong regardless of whose citizens it targets. The TikTok saga spoke to this clearly: Congress moved to ban the app specifically because Chinese intelligence could access American user data. TikTok was then effectively transferred to US-aligned ownership, but the surveillance apparatus underneath it didn't change at all. You're being equally exploited with no more rights.
- This is not a reason to abandon your VPN. Even if the NSA managed to collect your traffic, you would not be worse off than leaving it exposed to your ISP to log and sell freely. If you're exploring VPNs, our VPN Finder is a good place to start. Alternatively, our SPA Essentials have more trustless tools like Tor.
- Ultimately, the more people using privacy tools, the less targeted one person will be for using them. I strongly believe that using privacy tools is part of how we advocate for others who may need the tools even more than ourselves!
Bits & Bytes 🤖
~ LinkedIn Is Secretly Scanning Your Browser for 6,000+ Extensions
Every time you open LinkedIn in a Chromium-based browser, a hidden JavaScript routine silently probes your browser for more than 6,000 installed extensions, collecting sensitive hardware and software characteristics, encrypting the resulting fingerprint, and attaching it to every request you make. The practice, called "BrowserGate" is undisclosed in LinkedIn's privacy policy. The scan could expose whether you're quietly looking for work on the very platform where your current employer can see your profile, alongside extensions tied to religious practices, health conditions, and political orientation.
Our take: LinkedIn's defense is that it's protecting against scrapers and terms violations. (ha!) That sort of falls apart when the scan extends to religious tools, health apps, political extensions, and hundreds of competitor products with no connection to scraping.
Based on my research, Firefox and Safari users should not be affected by the extension scanning specifically as the script includes a isUserAgentChrome() gate that only fires on Chromium browsers. Brave's fingerprinting protection enabled can block the detection mechanism, as confirmed by one of the engineers I met at the ad-filtering dev summit. This is a reminder that using any privacy-focused browser is a critically-important step of any digital rights journey! LinkedIn just got caught, but it's happening on countless websites. What I haven't been able to confirm is if extensions-alone could have prevented this regardless of browser (Ex. Using uBlock Origin in Chrome)
~ 2.3 Million Android Devices Were Infected Through Google Play
A rootkit malware called NoVoice was hidden in over 50 apps on the Google Play Store, downloaded a combined 2.3 million times. The apps looked harmless (cleaners, games, gallery tools), required no suspicious permissions, and worked exactly as advertised. Behind the scenes, they exploited old Android vulnerabilities to gain root access, replaced core system libraries, and established persistence so deep that a factory reset won't remove the infection. Google has removed the apps and says devices with security patches from May 2021 or later are protected from the specific exploits observed.
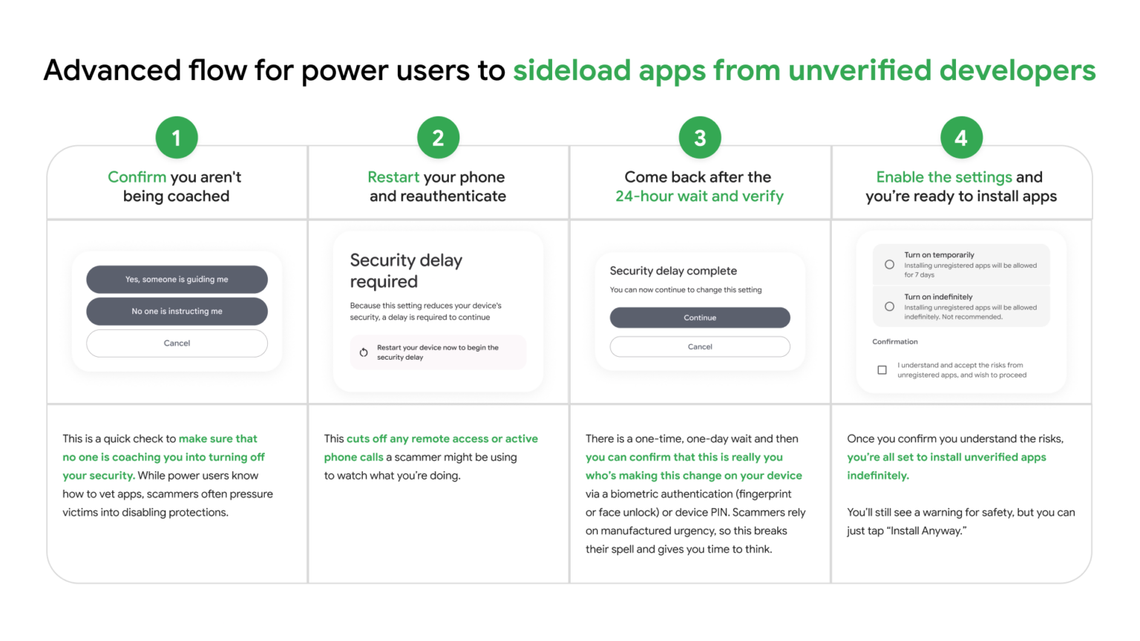
Our take: The irony here happens when we look at Google's justification for restricting sideloading on Android, the core argument being that the Play Store is a safer, curated environment. Keeping your Android device updated is the best individual defense here, but it's important to be honest about what the Play Store does and doesn't guarantee. We just wish Google would be honest as they propose these very reasons as justifications for attacking the openness of Android.
~ A Lawsuit Says Perplexity's "Incognito Mode" Is a Sham
A proposed class-action lawsuit alleges Perplexity AI has been sharing full conversation transcripts with Meta and Google since 2022, including when users had "Incognito Mode" enabled. The complaint describes embedded trackers (Meta Pixel, Google Ads, Conversions API) operating server-side, meaning no browser privacy setting can block them. Sensitive searches about health, finances, and legal matters were allegedly transmitted with personally identifiable information attached. The lawsuit covers users from December 2022 through early 2026. As of right now, Perplexity disputes the allegations.
Our take: Server-side tracking is specifically designed to bypass the tools privacy-conscious users rely on. Whether this lawsuit succeeds or not, it's a reminder that "private" labels on AI tools deserve the same skepticism you'd apply to a browser's incognito tab, where they rarely mean what most people assume. We are currently in the process of updating our SPA Essentials to include AI recommendations to offer alternatives going forward.
This Week on Techlore 📺
We spent this week building something we've been thinking about for a while: a unified SPA (Security, Privacy, Anonymity) ecosystem for our tools.
- SPA Essentials is your starting point—fast, actionable starter-pack advice. (It's what used to be our privacy resources)
- SPA Quiz is how you measure your progress over time in a fun, interactive manner.
- SPA Wiki is coming soon: a second brain for everything digital rights, think Wikipedia but for everything we discuss! It will be a living, breathing resource with top-tier information. This is inspired from my personal attempts of starting something semi-similar to this to centralize quality information in a single place.
- VPN Finder also got a proper name..."VPN Comparison Chart" wasn't exactly inspiring. It lives outside SPA but deserved better branding regardless.
Individual rewrites of each tool are coming in the next few weeks. If you have ideas for what else should live in the ecosystem, we'd love to hear them.
Finally: Surveillance Report and Techlore Talks have a new hosting provider. The redirect is clean, so no action required, but we'll be publishing updated RSS URLs shortly. If you hit any issues, swap to the new URL and you're good. But again, should happen automatically!
Action Item ✅
Section 702 of FISA, the surveillance law at the heart of this week's VPN story is approaching reauthorization. This is one of the most direct levers available for pushing back on mass surveillance, and it only gets renewed because most people never weigh in. Take five minutes this week to contact your representatives and tell them Section 702 reform matters to you. The EFF is doing coverage we all should watch carefully. Contact your reps & support the EFF!
Digital Rights Digest—threats to your freedom and how to fight back. A five-minute weekly read, 100% free.